-
Github: Getting the SHA256 fingerprint of an SSH key
2 min read
When you need to check the SSH key that you are using on your GitHub account, you'll get the SHA256 fingerprint of the key.
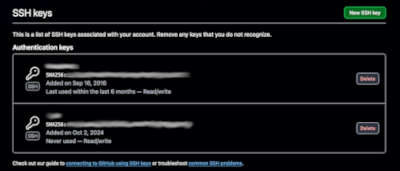
Depending on the version of OpenSSH that you are using, the fingerprint you get from using
ssh-keygen -lfmight be different from the one that GitHub shows you.22/10/2024
Read more... -
Getting started with Argo Workflows
6 min read

Argo Workflows is a open-source container-native workflow engine designed to run containerized jobs in Kubernetes clusters, similar to tekton.
It uses DAGs (Directed Acyclic Graphs) or step-based workflows that will run each in a container.
22/10/2024
Read more... -
AWS: An error occurred (Throttling) when calling
2 min read

When working with AWS, one might encounter errors related to throttling, such as:
Error: An error occurred (Throttling) when calling the GenerateServiceLastAccessedDetails operation (reached max retries: 4): Rate exceededThis error occurs when an AWS service has throttled your activity: the number of API requests made for that particular account and region have exceeded the rate limit allowed for that particular service.
10/10/2024
Read more... -
Understanding AWS IAM Permissions Boundaries
3 min read
AWS Identity and Access Management (IAM) is a critical service for managing access to AWS resources. Among its many features, Permissions Boundaries add an extra layer of control ro ensure that users and roles cannot exceed specific permissions, even if somehow can update their IAM policies.
08/10/2024
Read more... -
IAM Privileges: How to check what privileges are being used
3 min read

When we are working with IAM roles, it's essential to make sure that the permissions we are granting exactly what we need: No more, no less.
The AWS SDK provides a way to check what privileges are being used by a role, group, or user. This can help us to fine-tune the permissions we are granting and remove any unnecessary privileges.
07/10/2024
Read more...